Overview
Netgear G54/N150 Wireless Router WNR1000v3, firmware version 1.0.2.68 and possibly earlier, uses insufficiently random values for DNS queries and is vulnerable to DNS spoofing attacks.
Description
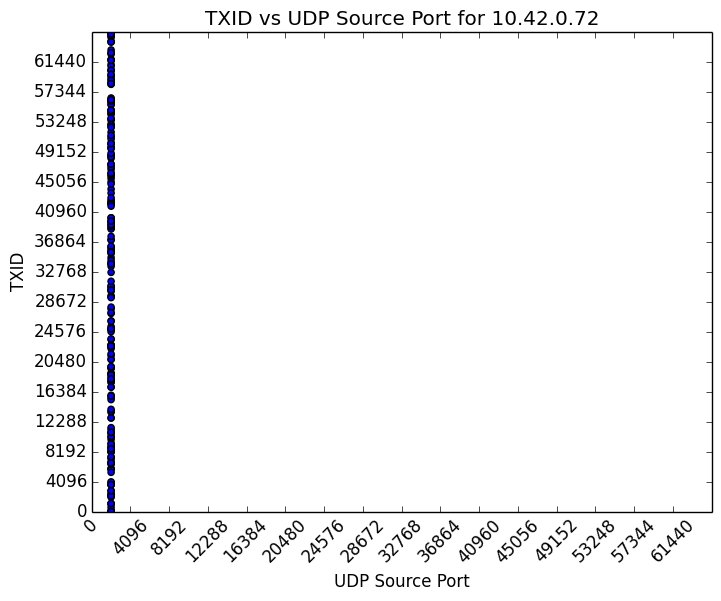
CWE-330: Use of Insufficiently Random Values - CVE-2015-8263 The Netgear G54/N150 Wireless Router WNR1000v3 uses static source ports for all DNS queries originating from the local area network (LAN). An attacker with the ability to spoof DNS responses can cause WNR1000v3 LAN clients to contact incorrect or malicious hosts under the attacker's control. |
Impact
A remote, unauthenticated attacker may be able to spoof DNS responses to cause WNR1000v3 LAN clients to contact attacker-controlled hosts. |
Solution
The CERT/CC is currently unaware of a practical solution to this problem. |
Vendor Information
CVSS Metrics
| Group | Score | Vector |
|---|---|---|
| Base | 5 | AV:N/AC:L/Au:N/C:N/I:P/A:N |
| Temporal | 4.5 | E:POC/RL:U/RC:C |
| Environmental | 1.1 | CDP:ND/TD:L/CR:ND/IR:ND/AR:ND |
References
Acknowledgements
These vulnerabilities were reported by Joel Land of the CERT/CC.
This document was written by Joel Land.
Other Information
| CVE IDs: | CVE-2015-8263 |
| Date Public: | 2015-12-10 |
| Date First Published: | 2015-12-10 |
| Date Last Updated: | 2015-12-10 15:45 UTC |
| Document Revision: | 7 |